Member-only story
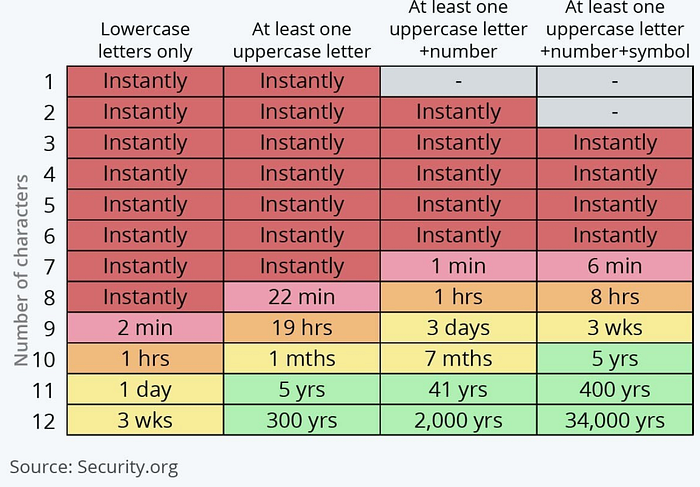
Those Tables With Password Cracking Times That Scare You And Peddle Snake Oil — Are Mostly Wrong!
Meet The Mighty PBKDF2 (Protector of Wifi and Your Password)
Education and snake oil?
In cybersecurity, you get those who pedal snake oil, and others that just try to scare you. The gap is that the advice is not given in an educated way, and basically just scares people (or gets them to buy the latest security product).
These days, the chances of someone cracking your password from a hashed version is likely to be minimal. For one, the chances of getting access to the hashed version of a password is extremely low, and for two, the password is typically stored in a way that will make it extremely costly — such as requiring the cost of electricity to boil a lake (or loch, in Scotland) — to crack it.
But, still, we get them from those who aim to “educate” (aka “preach”) us on Cybersecurity. Telling us not to share our passwords or to not click on spear-phishing links are better approaches than asking us to use long and complex passwords. As humans, we kinda lose it once we go over 10 characters. And, HashCat, too, knows all our little tricks for passwords (eg we typically always have one upper case letter, and put it at the start) — where so-called complex passwords can be just as easy to crack as short and simple ones.
And, too, the days of Microsoft Windows XP are past, but some still think we are living in that world. These days, even Microsoft uses encrypted passwords with a slow hashing method. Linux, too, uses the best of breed for its password hashing, and where it would cost you your mortage for a single bruite force password crack. The industry has moved on — and has learnt from its mistakes, but some are still stuck in the past.
Ask anyone who has forgotten their Bitcoin wallet password — and I get continual questions from many people about this — about how difficult it is to recover it though brute force…
