
Member-only story
ECDSA: Revealing the private key, from four signed messages, two keys and shared nonces (SECP256k1)
It’s well known that the ECDSA signature (as used in Bitcoin) needs to be carefully created, or the private key can be discovered. The nightmare would thus be to sign a few messages and for Eve to then discover the private key from these. In this case, we will look at the case where Alice has two key pairs and signs four messages with these, and for Eve to discover where private keys.
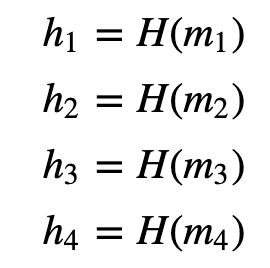
Alice will have two key pairs [1], and with two private keys (x_1 and x_2). She will sign message 1 (m_1) with the first private key (x_1), sign message 2 (m_2) with a second private key (x_2), sign message 3 (m_3) with the first private key (x_1) and sign message 4 (m_4) with the second private key (x_2) The same nonce (k_1 is used for messages 1 and 2, and another nonce (k_2) is used to sign messages 3 and 4. Now let’s say we have four messages (m_1 .. m)4) and have hashes of:
The signatures for the messages will then be (s1,r1), (s2,r1), (s3,r2), and (s4,r2):

Using Gaussian elimination, we can also recover the private keys with:
and:
Here is some code which discovers the private keys [here]:
import ecdsa
import random
import libnum
import hashlib
import sys
G = ecdsa.SECP256k1.generator
order = G.order()priv1 = random.randrange(1,order)
Public_key = ecdsa.ecdsa.Public_key(G, G * priv1)
x1 = ecdsa.ecdsa.Private_key(Public_key, priv1)priv2 = random.randrange(1,order)
Public_key2 = ecdsa.ecdsa.Public_key(G, G * priv2)
x2 = ecdsa.ecdsa.Private_key(Public_key2, priv2)k1 = random.randrange(1, 2**127)
k2 = random.randrange(1, 2**127)msg1="Hello"
msg2="Hello1"
msg3="Hello3"
msg4="Hello4"if (len(sys.argv)>1):
msg1=(sys.argv[1])
if (len(sys.argv)>2)…
